GSM networks in the US and Europe use the A5/1 stream cipher to ensure cellular calls cannot be listened into by unauthorized parties monitoring radio traffic. However, the guarantee of privacy is no longer ensured. New attack techniques were unveiled at the Hacking at Random conference in The Netherlends which would allow an attacker to decrypt cellular calls made over a GSM network. The attacker only needs the new software and about $500 in radio monitoring equipment. The AS5/1 cipher has been criticized for many years, but this is one of the first publicly available exploits to demonstrate the weaknesses first hand.

The presentation is here.
The A5/1 cracking project homepage is here.
GSM is used by many major cellular providers such as AT&T and T-Mobile (see GSM Coverage Map). The main alternative to GSM network is CDMA which is used by providers such as Verizon, Alltel and US Cellular (see CDMA World Map).
Impacts?
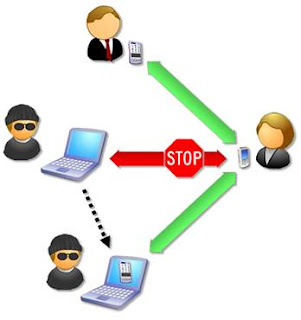
The ability to decrypt A5/1 encryption would enable an attacker to listen in to all cellular communications made over a GSM network. To execute the attack the attacker would need to be close enough to the target to monitor the radio waves emitted from the phone. However, this isn’t much of a restriction since the radio waves can be picked up from quite some distance.
This attack should raise serious concerns about the sensitivity of information exchanged over cell phones. An attacker with this equipment situated near a major corporate office or within a large city could easily glean very sensitive data from cellular voice calls.
Regarding data exchanged over cellular phones (e.g. 3G or EDGE), this shouldn’t really have any impact. All sensitive data should already be configured to use SSL/TLS or VPN for protection during transmission. Therefore, the attacker could break the A5/1 cipher, but they would only see encrypted data being exchanged. However, all data that is exchanged using clear text protocols (HTTP, telnet, ftp, etc) would be visible to the attacker. This is not much of a concern since there should not be any expectation of confidentiality when using a clear text protocol anyway.
About the attack
The attack leverages rainbow tables for a Time-Memory Trade-Off based attack. The A5/1 cracking project is enabling volunteers to help develop the rainbow tables for the A5/1 cipher and distributing the generated tables over bittorrent. Clever adaptations were made to the rainbow table generation to minimize the number of tables that were needed and thus dramatically reduced the required processing efforts.
This is a guest post by Michael Coates, a senior application security consultant with extensive experience in application security, security code review and penetration assessments. He has conducted numerous security assessments for financial, enterprise and cellular customers world-wide.
The original text is published on …Application Security…
Talkback and comments are most welcome
Related posts
Google Voice – No Privacy Remains?