
The new made-for-Netflix drama “House of Cards” is aptly named for what it represents — a fundamental shift in entertainment creation, distribution and consumption. The political thriller is by no means the first made-for-web TV show. But the production values, storytelling and intrigue meet, and in some ways surpass, those found from cable network productions. Yes, even Showtime’s popular “Homeland”.
I predict that Netflix has here what HBO did with “The Sopranos” in 1999, an industry-changing series. The D.C. drama, starring Kevin Spacey and Robin Wright, shows how the entertainment industry is a house of cards new media distribution can topple. Good content can go to the web first, or only there.
Crime Family
HBO was no studio startup when Tony Soprano sat in the psychiatrist chair 14 years ago, but had no real success producing television series (more mini-series and made-for-pay-cable feature films). The drama’s popularity demonstrated the value of pay cable, and bolstered the appeal and economics. All the cable productions that followed — even “Mad Men” or “Walking Dead”, from non-premium subscription network AMC — owe homage to “The Sopranos”.
Like HBO, Netflix depends on licensing deals with Hollywood studios, but the new media company also threatens long-established distribution channels. “House of Cards” spotlights the economics, suddenly showing how Netflix could be something like the Google of entertainment. The search giant’s business model is about giving away stuff for free — or at most for less cost — than competitors.
From that perspective, Google lowers the value of everything it touches. Why should people pay for something they can get for free? But that’s a simplification. Free isn’t often good enough. The stuff given away by Google has value — or is valuable enough.
People will always pay, and this is especially true for entertainment, when there is value. Why else do subscription services like HBO remain so popular? (Okay, that and some damn good content-distribution contracts.) That said, Netflix is just $7.99 a month, available to pretty much anyone — no cable or premium network subscription required. Like Google, Netflix changes the economics by streaming movies and TV shows — that’s nothing new. Producing dramas that are as good as those from HBO or Showtime raises the stakes.
Netflix seemingly bites the hand that feeds it, but that’s another simplification. People didn’t stop watching network television because of pay-cable dramas like “The Sopranos”. TV simply got better, and I’d argue across the board. A new golden age of television started around 2004, with debut of dramas like “Lost”, and continues today (Yes, there are early exceptions, like “The West Wing”, which is same vintage as “The Sopranos”, or many Fox dramas).
Network programs are better, but more importantly, cable is changed. Most major cable-only networks, even the non-premiums, produce in-house dramas, not just mini-series. If successful, “House of Cards” could — I predict will — lead to a surge in TV shows produced directly for the web. The series is that good.
Political Intrigue
Netflix has a real winner that smartly, and too accurately, captures Washington’s political intrigue — from the Capitol dome to the newsroom. “House of Cards” is based on a 1990 BBC program, which also is available on Netflix. So, you can watch both and compare, which I may do. Besides great acting and storytelling, the original Netflix series does something else quite dramatic. There is no serialization. All 13 episodes are available at once, for people to watch at their own pace. That’s simply brilliant.
“The world of 7:30 on Tuesday nights, that’s dead”, series director David Fincher says. “A stake has been driven through its heart, its head has been cut off, and its mouth has been stuffed with garlic. The captive audience is gone. If you give people this opportunity to mainline all in one day, there’s reason to believe they will do it”.
That’s how many people watch TV shows on Netflix, or even Amazon Prime, today. It’s the next thing beyond the DVR. Rather than time-shift by recording, watching and fast-forwarding commercials, people can watch what they want when they want and how much they want. Granted, this isn’t new, whether programs are rented, purchased or consumed for free from the Internet.
The earth that shakes media distribution’s house of cards is something else: Releasing all episodes of a series simultaneously, turning the concept of serialization on its head. My wife and I watched the first two “House of Cards” episodes late last night and probably more today.
For Netflix, the approach makes loads of sense, because the business model is different. For traditional television programming, the idea is to get people to come back and to pull them away from competing networks. Like websites that measure value by the amount of time people stay on them, Netflix wants viewers to stay put. Why not 13 hours straight, then present them even more reasons with other programming that is either original or otherwise not available elsewhere.
Take “Annika Bengtzon: Crime Reporter“, which I recently watched on Netflix. The producers filmed six 90-minute movies back-to-back over the course of a year. Only one released to theaters in Europe. But all are quite good and available on Netflix to watch on your time, which I did when sick with the flu earlier this month. The production concept is similar to “House of Cards” — make them all, then release them all, at the same time. I highly recommend the book-based Swedish series, by the way.
The question, looking ahead 12 to 36 months: What next, and from where? I’d pay for MAX Go, as a separate streaming service, just for the original programming. Cut cable’s cord. Wouldn’t you? Today you can taste the future. “House of Cards” debuted February 1, and for the month the first episode is available to everyone, even non-subscribers.

 If there’s an aspect of your PC which you don’t like then it can normally be changed very quickly: a right-click option here, maybe launch a Control Panel applet there, install a new program perhaps, and the system should soon be more suited to your needs.
If there’s an aspect of your PC which you don’t like then it can normally be changed very quickly: a right-click option here, maybe launch a Control Panel applet there, install a new program perhaps, and the system should soon be more suited to your needs.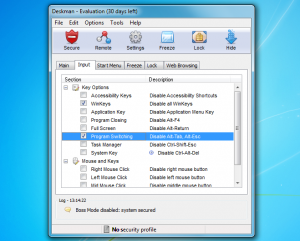 You might start by building a Safe Start Menu, for instance, with only the applications you’d like your users to access. The regular Start Menu can then be hidden (although it still exists, if you need to use it yourself later).
You might start by building a Safe Start Menu, for instance, with only the applications you’d like your users to access. The regular Start Menu can then be hidden (although it still exists, if you need to use it yourself later).








 AVAST Software has released the first public beta of avast! 8 (or the first official one, anyway). Downloads are available for
AVAST Software has released the first public beta of avast! 8 (or the first official one, anyway). Downloads are available for 









 Santa Claus and UFOs may indeed have something in common. As Michael Shermer shared at TED2010, they are two things that engage the “belief engine” that is also known as our brains.
Santa Claus and UFOs may indeed have something in common. As Michael Shermer shared at TED2010, they are two things that engage the “belief engine” that is also known as our brains. Michael Shermer: The pattern behind self-deception
Michael Shermer: The pattern behind self-deception