By Scott M. Fulton, III, Betanews
In an astonishing statistic released this morning, Web analytics service Experian Hitwise reported that of all the Web searches performed in the United States on the top three search engines Google, Yahoo, and Bing during the first four weeks of March, about two percent on average are for the word facebook. For Yahoo and Bing, Another one percent is for facebook.com, and just less than one percent is for facebook login.
Coupled with statistics for the same month from analytics service comScore, Experian’s findings suggest that, from March 1 through March 27, searches for a way to get to Facebook other than through typing the address or clicking on a bookmark, accounted for as many as 175.84 million Google searches in the US, over 78.9 million Yahoo searches, and over 80 million Bing searches.
That means an estimated 2.2% of Americans’ Web searches are for their Facebook front page.
Before one goes chocking this figure up completely to massive user inexperience: Although typing facebook into the address bar of Firefox brings up the home page of Facebook.com, typing facebook into the address bar of Internet Explorer and Google Chrome brings up results for a Web search for Facebook using the browser’s default search engine, which for many users is typically Google.
On the other hand, it’s difficult to ignore that — once again coupling Experian’s and comScore’s numbers — some 18.5 million Yahoo searches, and nearly 20.2 million Bing searches, in the US for the first four weeks of March, were for google.
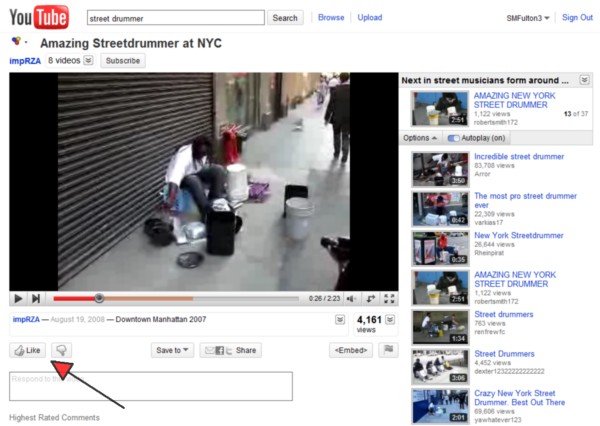
The fact that tens of millions of searches every month are for the location of one of the most obvious Web portals on the planet, posed a problem for a very legitimate news site, ReadWriteWeb, last February. A news article whose headline was “Facebook Wants to Be Your One True Login,” ostensibly about the social service incorporating friends lists from multiple other services, became one of the leading search results on Google and other sites, for users typing facebook login.
The result was pandemonium, as thousands of folks confused about their new destination, commented to ReadWriteWeb wondering where their Facebook had gone…and worse, lamenting the fate of all their farm animals and crops they had tended to in the game of Farmville, a Facebook app that demands persistent participation.
But what’s even more astonishing is that the parade of confused participants continues even as late as today (April 28), some eleven weeks after the article’s original date of publication. Commenters (some for real…some perhaps pretending) continue to protest against what they believe to be a change in Facebook’s format, including redecorating from blue to red, still pleading, “How do I log in?” Protesters join a sea of equally sad lampooners ridiculing the confused patrons along with, more recently, unsolicited advertisements from attention seekers.
Learning the lesson from this experience and leveraging their own gains from it, a number of sites have renamed or retitled themselves “Facebook Login,” or something similar. Despite even that fact, the ReadWriteWeb article continues to be the #6 search result that Google provides, for the estimated 85.4 million US users who type facebook login every month.
That figure is astonishingly close to the number of people that Farmville reports as active users, as Web analyst and blogger Justin Kistner reported last month. Also putting two and two together, Kistner noted that the number of people Facebook reports to be playing Farmville in March (83.2 million) exceeds the number of people believed by independent estimates to be using Twitter (75 million).
Thus, if you couple these figures, the number of people who can’t find Facebook outnumber those who can find Twitter.







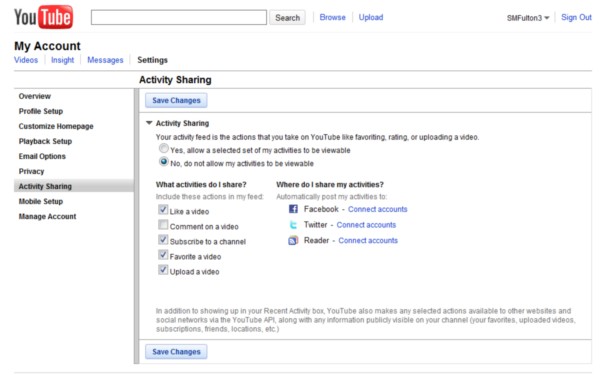
 Amid news yesterday of a discovery by an independent programmer of what appeared to be another door left open for Web apps to access Facebook users’ personal data, Sen. Chuck Schumer (D – N.Y.) called upon the Federal Trade Commission to take the next step in forming the equivalent of a US “privacy commissioner.”
Amid news yesterday of a discovery by an independent programmer of what appeared to be another door left open for Web apps to access Facebook users’ personal data, Sen. Chuck Schumer (D – N.Y.) called upon the Federal Trade Commission to take the next step in forming the equivalent of a US “privacy commissioner.”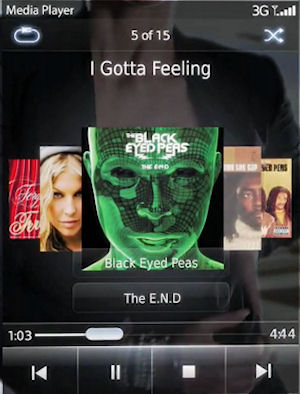

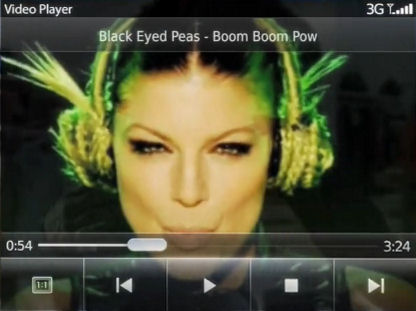

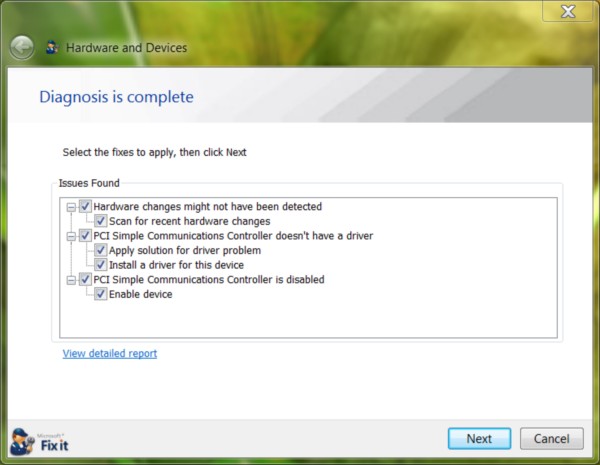
 One of Silverlight video’s biggest advantages to date has been the server’s ability to tweak the bitrate of video playback as it’s being played back, and as the bandwidth of the connection varies. It’s the
One of Silverlight video’s biggest advantages to date has been the server’s ability to tweak the bitrate of video playback as it’s being played back, and as the bandwidth of the connection varies. It’s the 

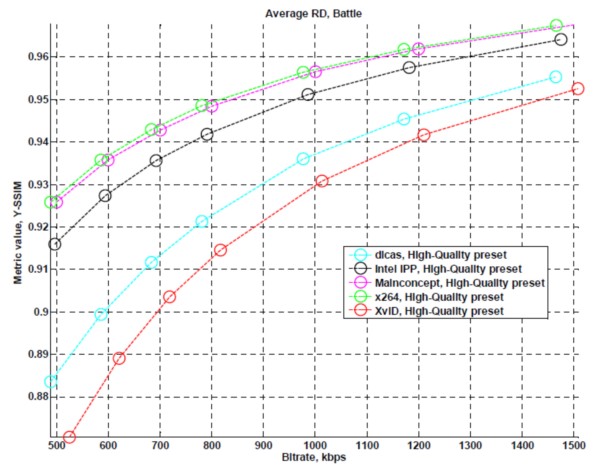
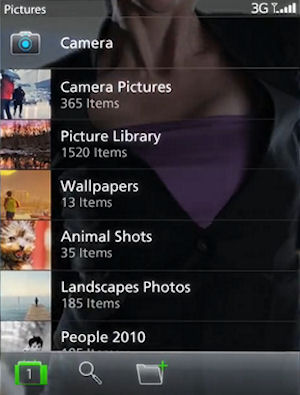
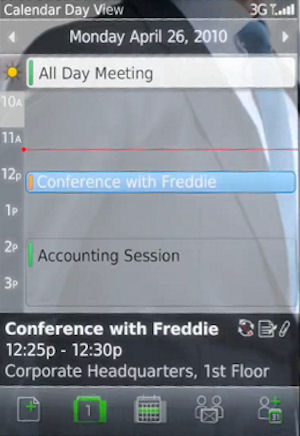
 The Pearl’s appeal to date has been its form factor — not wide like a sandwich loaf slice, but thinner than a bar of soap. The tradeoff has been the keyboard: There’s not enough room for the traditional BlackBerry QWERTY, so the new Pearl 9100 features a 20-key layout that, for some, takes some getting used to. An optional Pearl 9105 model includes a more traditional 14-key layout.
The Pearl’s appeal to date has been its form factor — not wide like a sandwich loaf slice, but thinner than a bar of soap. The tradeoff has been the keyboard: There’s not enough room for the traditional BlackBerry QWERTY, so the new Pearl 9100 features a 20-key layout that, for some, takes some getting used to. An optional Pearl 9105 model includes a more traditional 14-key layout.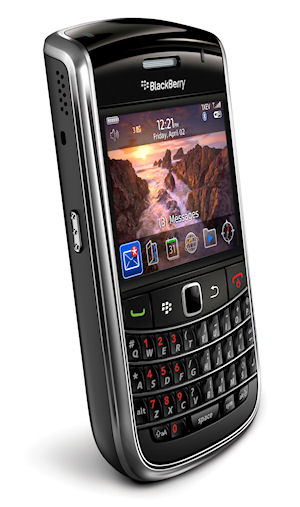 Yet the 9650 isn’t decked out like the 9700, or even like the new Pearl — it’s not really a 3G phone. When RIM says it “supports” 3G, it’s referring to EV-DO, which is a bit more like “2.5G.” It’s a CDMA phone, and will premiere in the US on Sprint.
Yet the 9650 isn’t decked out like the 9700, or even like the new Pearl — it’s not really a 3G phone. When RIM says it “supports” 3G, it’s referring to EV-DO, which is a bit more like “2.5G.” It’s a CDMA phone, and will premiere in the US on Sprint.
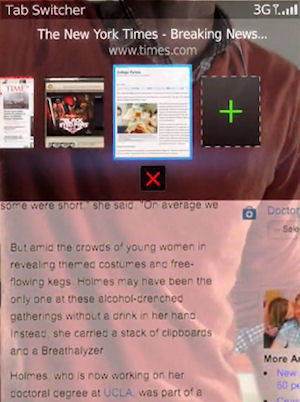
 While bitterness continues over the implications of Sections 3.3.1 through 3.3.3 of Apple’s recently modified Developers’ Agreement (
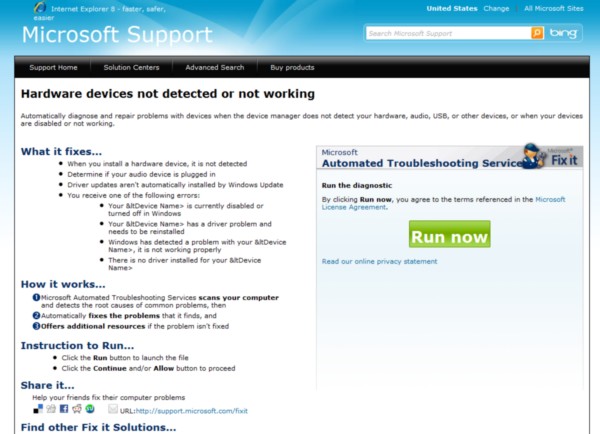
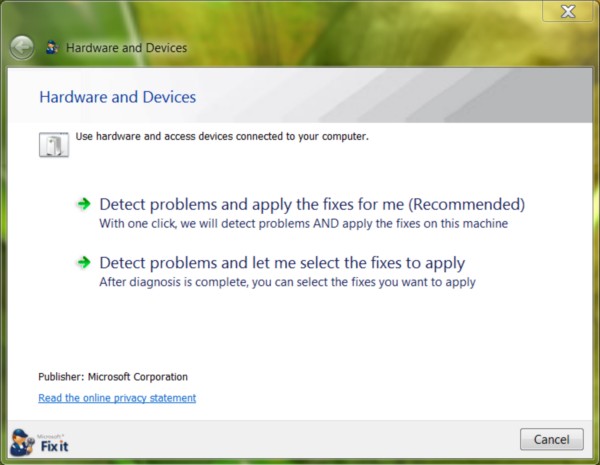
While bitterness continues over the implications of Sections 3.3.1 through 3.3.3 of Apple’s recently modified Developers’ Agreement ( Many instances of malware on Windows-based systems masquerade themselves as system services — the various independent processes that respond to requests from both the operating system and applications with functions that users typically need. Network connectivity and printing are among the more common Windows services; and if you’ve ever perused the processes list of Task Manager (or, better yet,
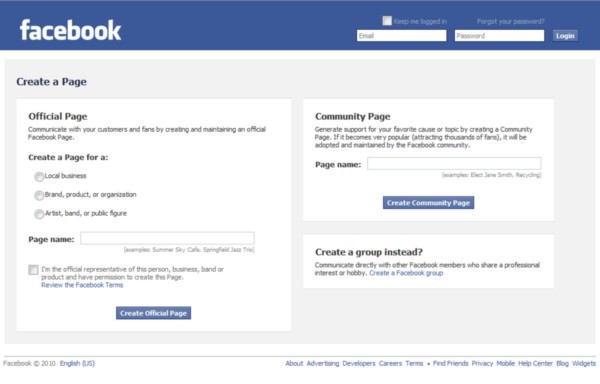
Many instances of malware on Windows-based systems masquerade themselves as system services — the various independent processes that respond to requests from both the operating system and applications with functions that users typically need. Network connectivity and printing are among the more common Windows services; and if you’ve ever perused the processes list of Task Manager (or, better yet,  “Today, the Web exists mostly as a series of unstructured links between pages. And this has been a powerful model, but it’s really just the start,” said Zuckerberg. “The Open Graph puts people at the center of the Web. It means that the Web can become a set of personally and semantically meaningful connections between people and things. I am friends with you. I am attending this event. I like this band. These connections aren’t just happening on Facebook, they’re happening all over the Web. And today, with the Open Graph, we’re going to bring all of these together.”
“Today, the Web exists mostly as a series of unstructured links between pages. And this has been a powerful model, but it’s really just the start,” said Zuckerberg. “The Open Graph puts people at the center of the Web. It means that the Web can become a set of personally and semantically meaningful connections between people and things. I am friends with you. I am attending this event. I like this band. These connections aren’t just happening on Facebook, they’re happening all over the Web. And today, with the Open Graph, we’re going to bring all of these together.”