I woke up one morning about four weeks ago and realized in a flash that I’d hit a wall. Most days I can’t wait to get to work. On this day, I struggled to get myself out of the house.
The first three months of the year had been intensely demanding, between hiring a series of new employees for a rapidly growing business, working with colleagues to develop several new products, traveling frequently, and taking on multiple writing assignments.
One of the primary principles of the work we teach at the Energy Project is that the greater the performance demand, the greater the need for recovery. I needed a vacation, but what I needed most of all was a period of total digital disconnection. My brain felt overloaded and I needed time to clear it out.
My wife and I made reservations to go to our favorite hotel for nine days. But I knew that getting away from my office wouldn’t be enough if I remained tethered to my online life and my work. I decided not to bring my laptop, my iPad, or my cellphone. I left an away message that made it clear I wouldn’t be checking email.
I was determined to eliminate temptation to the maximum extent possible. I had learned from past experiences how easy it is for me to succumb, given the opportunity.
As Daniel Goleman writes in Focus: The Hidden Driver of Excellence, a fascinating new book he’ll publish this fall: “Overloading attention shrinks mental control. Life immersed in digital distractions creates a near constant cognitive overload. And that overload wears out self-control.”
From the moment I boarded the plane for our trip, I noticed a shift. Ordinarily, I would have skittered between reading the newspaper, magazines, answering email, and surfing the web (if it was available). I’d brought along a pile of books, mostly novels, and none of them related to work. I began reading the first one, and I very quickly became absorbed. For once, nothing else was competing for my attention.
The first time I felt a distracting impulse, it was to Google something I’d read. The initial pull was compelling, but I let it pass. Over the next several days, it happened perhaps a half-dozen more times, and on each occasion I simply observed the feeling without responding to it. By mid-week, that impluse evaporated, and I realized how much richer and more satisfying any experience is when it’s not interrupted — even if the interrupter is me.
It turned out there were no newspapers at our hotel. My first response was a bit of panic — I’ve read The New York Times daily since I was a teenager — but soon, I realized I was giving up the fix of more information that I didn’t really need.
Instead, I became increasingly aware that the relentless diet of information I ordinarily consume leaves me feeling the same way I do after eating a couple of slices of pizza or a hot dog and French fries — poorly nourished and still hungry.
What grew each day was my capacity for absorbed focus. For months now, I’ve wanted to read Far From the Tree, Andrew Solomon’s book about the challenges of parenting children with disabilities such as dwarfism, Down’s syndrome, and deafness. The problem is that it’s nearly 1,000 pages long, and who has the time or the wherewithal for that? But with my mind freed of distractions, I found it easy to dive in, and read most of the book over a couple of days. The book was fascinating.
I had a similar experience on the tennis court. I’ve been taking lessons and working on my game all of my adult life, but on vacation last week, I was able to slow down and analyze my strokes with a wholly different level of patience and unhurried interest. It was the sort of learning you simply can’t do when you’re thinking about 10 other subjects.
By the end of nine days, I felt empowered and enriched. With my brain quieter, I was able to take back control of my attention. In the process, I rediscovered some deeper part of myself.
If there had been an emergency while I was away, I could have been reached. The humbling truth is that not a single thing demanded my attention. Most everything can wait.
I did finally feel ready to return to my everyday world — even enthusiastic to read my email and check my favorite websites. But I also felt less anxious urgency about dealing with what ordinarily feels so pressing.
The break deepened my recognition that chunks of time away from digital life are critical both to renewal and to work itself. In that spirit, I’ve committed to two rituals going forward. Twice a week — including this morning — I’m spending the first several hours of the day at home, working on projects that require focused attention, with my email and internet turned off. At the end of each work day, I’m going to spend at least a half-hour reading — and savoring — a book. The key to being more fully absorbed is to regularly and fully disconnect.
 Following the lead of a number of high-profile companies like
Following the lead of a number of high-profile companies like 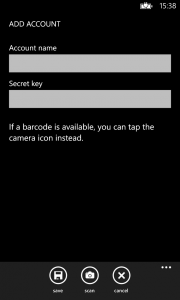 The app is called
The app is called 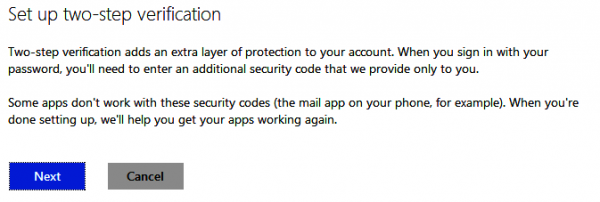
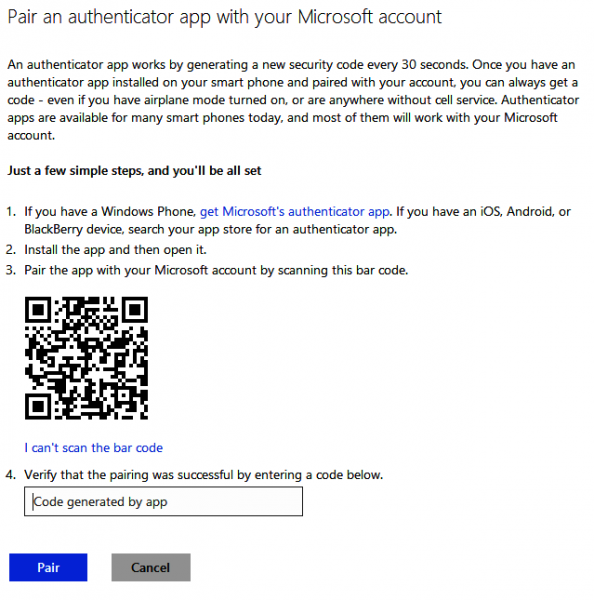


 This may seem a bit ironic, given that Xbox Live spent much of last Saturday
This may seem a bit ironic, given that Xbox Live spent much of last Saturday  Bill Kleyman
Bill Kleyman







