By Joe Wilcox, Betanews
On Friday, ComScore reported that in September, worldwide, Internet users spent more time at Microsoft sites than at Google, Yahoo or even Facebook. It’s an amazing statistic that has questionable street cred. ComScore has presented the data in a favorable way to Microsoft but which doesn’t accurately represent exactly how Internet users really spend time on popular Websites.
Time-spent-online data is hugely important to Microsoft and other popular destinations, such as Facebook, Google or Yahoo. While bloggers and news organizations obsess over every pageview, time spent online is a much more important metric. People coming and staying for hours is potentially more valuable to online advertisers than Internet users who click in and click out, which too often is the only measurable value of pageviews.
How people spend their time online is important, too. There — when read between the lines — ComScore’s data has some value for Microsoft. Are site visitors reading blog posts or news stories? Banner advertising and contextual search keywords could be effective. Are they playing interactive games with other Internet users? Contextually relevant ads within games could be better. Are they chatting with friends via IM or social status updates? Banner ads and interactive surveys might be more effective.
Time after Time
ComScore claims that worldwide during September, Microsoft sites accounted for 14.5 percent of the time spent online, followed by Google at 9.3 percent. What a strange perspective. After so many months — years — of Microsoft trailing Google by huge amounts, roles are decidedly reversed. But in the United States, Google and Yahoo led Microsoft, which overwhelming dominated online time in Europe,Latin America and Middle East (see first chart), ComScore claims.
The ComScore report is big on “What?” or “How much?” but offers scant reasons on “Why?” that makes the data relevant. The reasons are hugely important for understanding how consumer Microsoft marketing and new product releases could be paying off. Additionally, the phenomenon could show where Microsoft could leverage against Google and how Yahoo might be fumbling. I couch with “could” and “might” because of the caveats coming in the next two paragraphs.
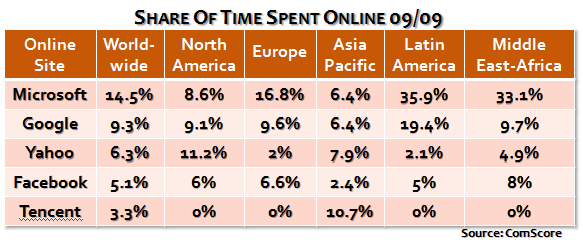
The ComScore data, while important for Microsoft, is incomplete. ComScore excludes Internet cafes, public computers and smaller mobile devices, such as cell phones, PDAs and smartphones. Internet cafes could be good for Microsoft because of some emerging markets, where the MSN and even Windows Live brands are strong; ditto for Yahoo. Public computers, if these count education institutions, could be good for Google. Cell phones and smartphones are a grabbag.
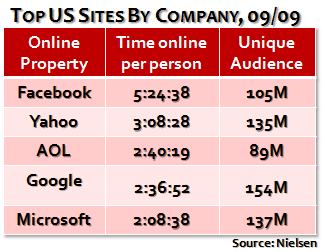
The data also is unspecific in a crucial area: How much actual time did individuals spend online. ComScore findings are in aggregate. For perspective, back in February, AOL and Yahoo led with most time online per Internet user, according to Nielsen. Per individual: 3:58:22 (hours, minutes, seconds) for AOL but only 2:16:54 for Microsoft. Caveat: Nielsen’s data only measures United States, while ComScore offers worldwide view. That said, U.S. data is inconsistent between the online analysis firms, too (see both charts).
Nielsen’s most recent data, also for September, shows Microsoft sites as No. 5 not No. 3 in the United States (see chart 2). Nielsen’s data is inconsitent with ComScore’s findings. AOL, which ComScore ranks No. 3 in the United States doesn’t show up at all in ComScore’s US rankings. Most startling, ComScore puts Facebook at No. 4 for time spent online among US Internet users, while Nielsen ranks Facebook as No. 1.
Facebook’s placement is hugely significant. In February, the social networking site didn’t even make Nielsen’s US top five. Now Facebook is tops, with time-spent-online per individual a whopping 5:24:38. Right, almost five-and-a-half hours per Internet user. Something else: Nielsen shows time online at Microsoft sites going down by about 8 minutes between February and September. By comparison, time online at Google sites rose about 40 minutes, nudging ahead of Microsoft.
Means to a Measure
Metrics and measurement mean everything for online data such as this. But to companies like Facebook, Google or Microsoft, marketing matters more. Microsoft will gain immeasurable PR value from ComScore’s study. But Nielsen’s consistency tracking time online — and measurement per individual — is more credible. Then there is the “Why?” ComScore does give, which makes sense of its approach to measuring time spent online at various Websites. Quoting the ComScore press release — a rarity for me:
Mearly 27 billion hours were spent on the Internet globally by a record online population of 1.2 billion Internet users age 15 and older. Microsoft Sites accounted for 14.5 percent of total minutes spent online in September, making it the most engaging global property, with Microsoft’s Windows Live Messenger representing nearly 70 percent of time spent on the property during the month.
Whoa. Seventy-percent came from Windows Live Messenger? Exactly how does usage of Microsoft’s desktop IM client count as time spent on the company’s sites? Surely only a fraction of Live Messenger users come through the the Web-based version, based on Microsoft data about client downloads. I ask again: How does time spent in Live Messenger count as time at Microsoft sites? Windows Live log-ins perhaps?
Maybe Safeway or Trader Joes should tally everyone using one of their shopping bags in monthly store customer counts. Perhaps Visa should count everyone using its cards to buy products as visitors to its Website. How about beauty product companies like Clinque, Mac or Sephora count every free product sample as customer purchase.
Something about ComScore’s data — at least as presented — doesn’t make sense.
Still, behind the measure, Microsoft can gain valuable insight. Windows Live Messenger is an arguably hot on-desktop/online property. It’s real estate Microsoft could connect to other properties, particularly broader Windows Live services or Windows 7.
To reiterate, ComScore’s data is questionably valid as presented (other than for Microsoft marketing purposes) because:
- ComScore ignores public PCs, Internet cafes, PDAs and smartphones
- The measurement is aggregated rather than for individual time spent online
- Windows Live Messenger accounts for 70 percent of the time spent at Microsoft sites
- Nielsen data, which does track individual time spent online, is more consistent over many months and contradicts some ComScore’s findings.
So, Betanews readers, I have to ask: Where do you spend most of your time online? Gulp, I would hope it would be Betanews. Comments are open for your answer.








 Happy post-Halloween! Thanks for sending in your costumes and thanks, most of you, for following the rules. That said, I’m proud to show you the 11 best costumes in this line-up, as judged by all of us at CG. I added one extra because we just couldn’t bear to choose between the various Iron Men we saw.
Happy post-Halloween! Thanks for sending in your costumes and thanks, most of you, for following the rules. That said, I’m proud to show you the 11 best costumes in this line-up, as judged by all of us at CG. I added one extra because we just couldn’t bear to choose between the various Iron Men we saw. O2 just announced what seems like a fairly magnanimous gesture on its part today, in preparation for the launch of the iPhone on other UK carriers and the end of iPhone exclusivity in that country. That should mean that O2 customers who want to take their business elsewhere can have their phones unlocked as early as tomorrow, since Nov. 10 is the stated launch date for Orange UK’s iPhone offerings.
O2 just announced what seems like a fairly magnanimous gesture on its part today, in preparation for the launch of the iPhone on other UK carriers and the end of iPhone exclusivity in that country. That should mean that O2 customers who want to take their business elsewhere can have their phones unlocked as early as tomorrow, since Nov. 10 is the stated launch date for Orange UK’s iPhone offerings.
 The first iPhone worm has been discovered. It comes to us via Australia, and appears to be limited to that country for now, although it has the potential to spread. It also stars Rick Astley, so to speak. The work changes the iPhone’s wallpaper to an image of the 1980s pop singer, who’s enjoyed a recent resurgence thanks to the
The first iPhone worm has been discovered. It comes to us via Australia, and appears to be limited to that country for now, although it has the potential to spread. It also stars Rick Astley, so to speak. The work changes the iPhone’s wallpaper to an image of the 1980s pop singer, who’s enjoyed a recent resurgence thanks to the 










 The US Supreme Court is hearing oral arguments this afternoon in the case of a pair of inventors who produced a formula for enabling energy commodity companies to manage the costs of energy that is often both bought and sold at fixed prices as “hedges” against future fluctuations. If you’re thinking, what in the world has that to do with information technology, the outcome of this case — whatever it is — will have a tremendous impact on the IT industry, particularly with respect to companies that hold intellectual property portfolios.
The US Supreme Court is hearing oral arguments this afternoon in the case of a pair of inventors who produced a formula for enabling energy commodity companies to manage the costs of energy that is often both bought and sold at fixed prices as “hedges” against future fluctuations. If you’re thinking, what in the world has that to do with information technology, the outcome of this case — whatever it is — will have a tremendous impact on the IT industry, particularly with respect to companies that hold intellectual property portfolios.